GSB PROJET
It's a project carried out in class in order to pass the E5 exam of the HND.
Our mission is :
Create a network infrastructure for GSB
The Galaxy Swiss Bourdin (GSB) laboratory is the result of a merger between the American giant Galaxy (specializing in viral diseases including AIDS and hepatitis) and the European conglomerate Swiss Bourdin (working on more conventional drugs), itself already a union of three smaller laboratories. In 2009, the two pharmaceutical companies joined forces to create a stronger entity in this industrial sector. Galaxy Swiss Bourdin Europe is headquartered in Paris.
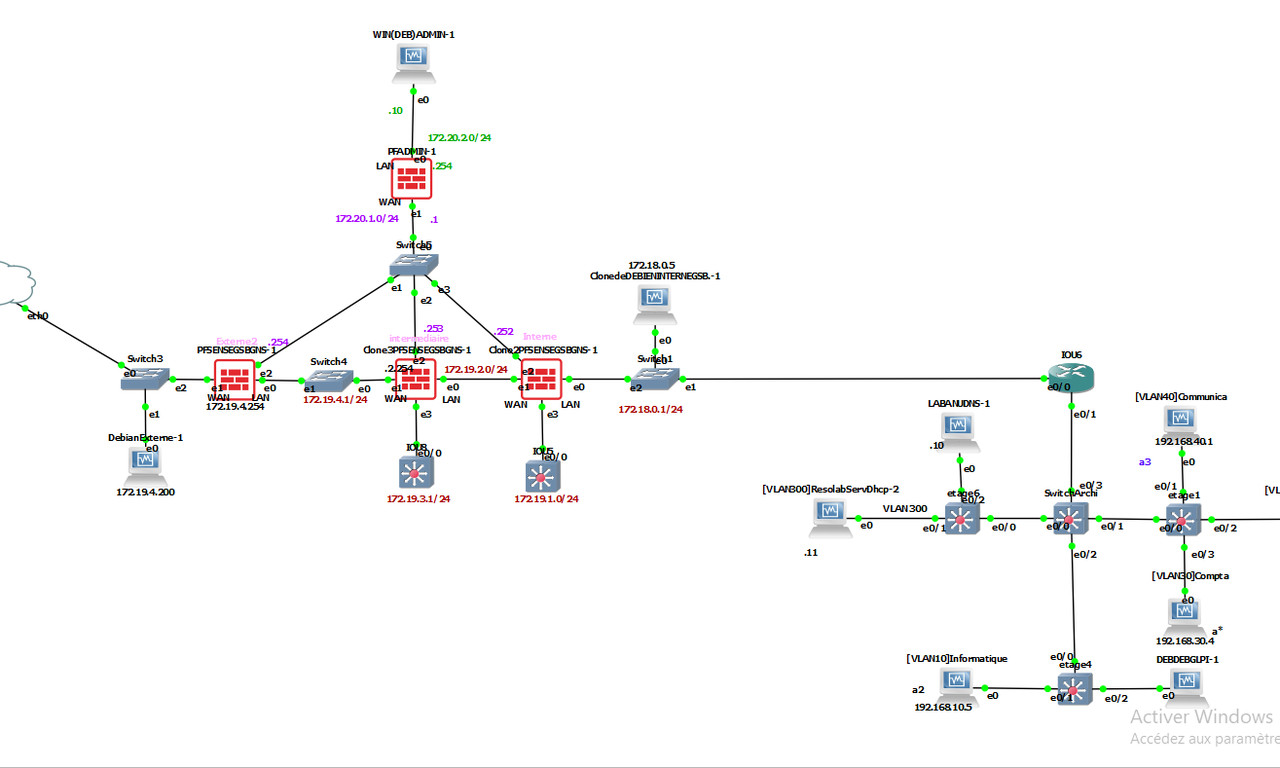
The network infrastructure is divided into several segments, each with a specific function:
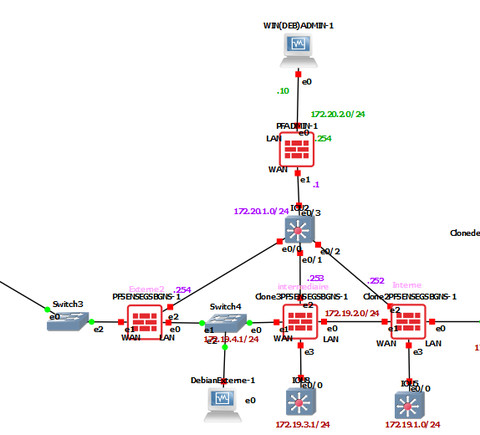
- PFsense firewalls: Two firewalls ensure network security and segmentation. They connect the WAN (external) and LAN (internal) networks.
- Central router (IOU6): Manages the interconnection between different VLANs and routes them to the appropriate zones.
- VLANs:
- VLAN 40: For communication (IP: 192.168.40.x).
- VLAN 10: For IT (IP: 192.168.10.x).
- VLAN 800: DHCP server (IP: 192.168.10.11).
- VLAN 300: Machine "LABANUDNS-1" (IP: 172.18.0.x).
- Machines and Servers: Debian and Windows machines are distributed over different subnets for specific needs (administration, testing, etc.).
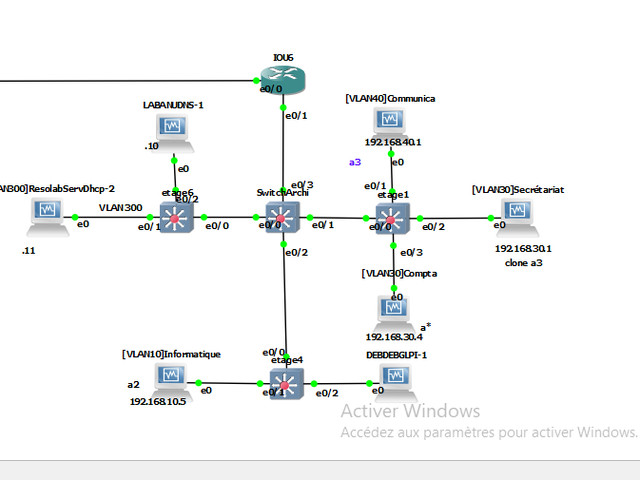
Inter-VLAN routing with IOU6
IOU6 = level 3 router:
Manages routing between all VLANs: VLAN10, VLAN20, VLAN30, VLAN40, VLAN300.
Each logical interface (sub-interface) on e0/1 corresponds to a VLAN:
→ VLAN10 (IT): 192.168.10.5
→ VLAN40 (Communication) : 192.168.40.1
→ VLAN30 (Secretariat) : 192.168.30.1
Objective:
Allows PCs in different VLANs to communicate with each other via IOU6.
Can apply inter-VLAN security rules (via ACLs if required).
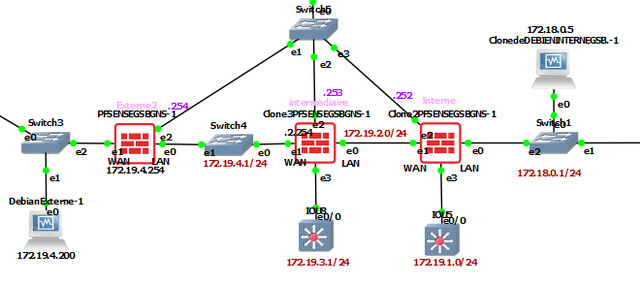
Internet access and flow security
DebianExterne-1 = Simulates the Internet:
Connected via Switch3 to a pfSense (WAN).
The firewall acts as a security gateway, enabling:
NAT: translates internal IPs to its external IP.
Filtering: blocks or allows flows to/from the Internet.
Security:
Each pfSense controls a domain:
pfSenseGSBGS1 → Manages 172.19.20.0/24
pfSenseGSBGS2 → Manages 172.20.0.0/24
This breakdown enables layered security, often used in business.
DMZ & Firewall
My DMZ is represented by the 172.19.20.0/24 network. It can be located here :
Connected between two pfSense :
pfSenseGSBGS1 (WAN: 172.19.4.254, LAN: 172.19.20.1)
pfSenseGSBGS2 (WAN: 172.19.20.254, LAN: 172.20.1.1)
Operation :
The 172.19.20.0/24 network acts as a buffer zone (DMZ).
Incoming traffic from "Internet" (external Debian) passes through pfSenseGSBGS1.
This traffic can be redirected to services hosted in the DMZ.
If traffic is allowed to continue to the LAN (172.20.0.0/24), it must pass through pfSenseGSBGS2, which filters it again
